
What are Insider Threats?
It’s no secret that insider threats have been, and continue to be, an expensive problem for companies of all sizes in the current hyperconnected marketplace. When all your focus is set on …
Discover valuable insights and expert analysis on IT assessments and cybersecurity in the RapidFire Tools Blog. Stay ahead with practical tips and trends for MSPs, IT professionals, and businesses, ensuring effective defense against cyber threats and delivering exceptional IT services.

It’s no secret that insider threats have been, and continue to be, an expensive problem for companies of all sizes in the current hyperconnected marketplace. When all your focus is set on …

When we send staff into the field, we often don’t get much feedback unless it’s a negative experience. When those complaints roll in, we get a pretty good idea of what’s gone wrong …

We frequently get questions about the difference between network assessment tools and remote monitoring and management (RMM) software. “Why would/should we add an IT assessment solution?” clients ask. …

As cybercrime continues to expand at an alarming rate, MSPs need to proactively seek new solutions to protect clients and deter attacks. Offering vulnerability scanning should be the minimal baseline …

Savvy MSPs know IT assessments are not only useful in prospecting and closing new clients, but it’s also fantastic when it comes to scoping and quoting existing business. Performing IT …
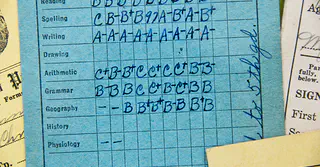
No, not the old school kind that we angsted over in school. And the client doesn’t need to get their parent to sign it either. This report presents a consolidated view of your client’s …

Network assessments are a unique and effective offering under the “network security” umbrella. A network assessment tool doesn’t simply monitor a network like RMM software does. It provides …
On-premise Microsoft Exchange servers are a growing target for cyberattacks due to the vulnerabilities in the software. The fact it is difficult to patch and update only adds to the threat. Since …

Businesses that don’t identify and remediate vulnerabilities in their IT environments are easy targets for cybercriminals or malicious insiders. Given today’s cyberthreat landscape, not …